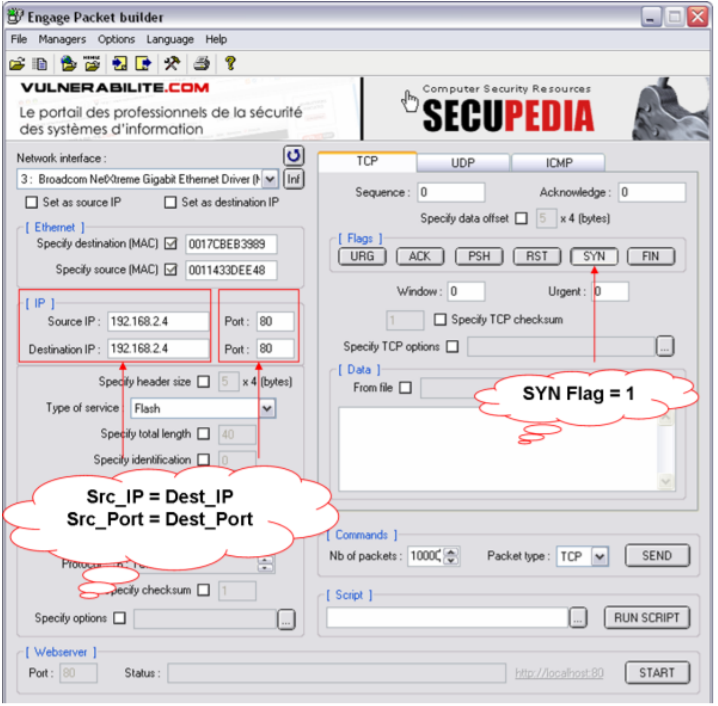
TurkHackTeam EN on Twitter: "Land Attack❗ #cybersecurity #cyberattack #data #attack #attacker #system #machine #network #tcp #ip #dos #ddos #land #web #website #files #cybercrime #hack #hacker #hacking #turkhackteam https://t.co/fpY9A4MfKr" / Twitter

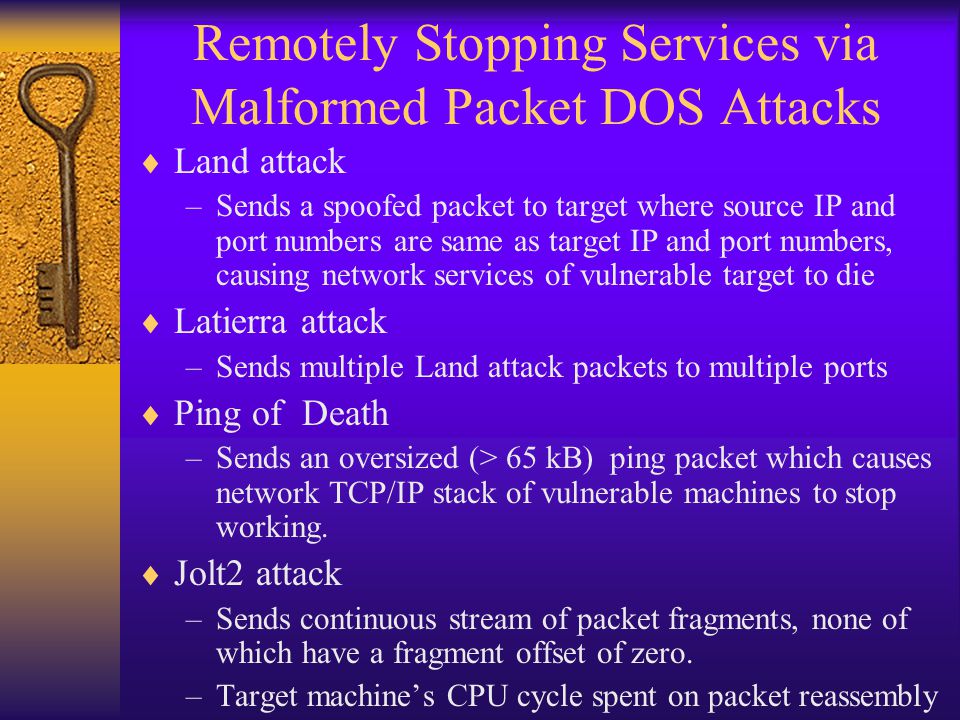
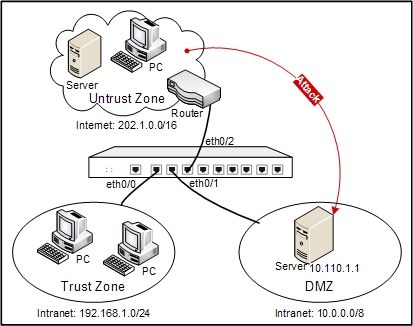
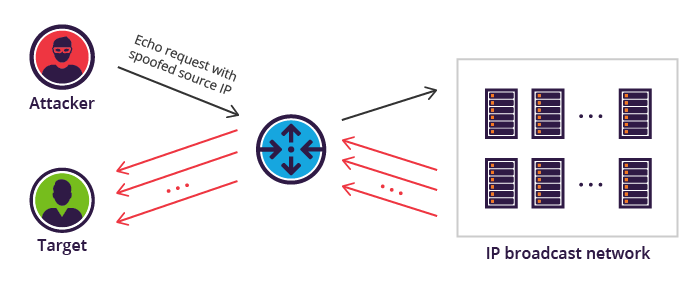
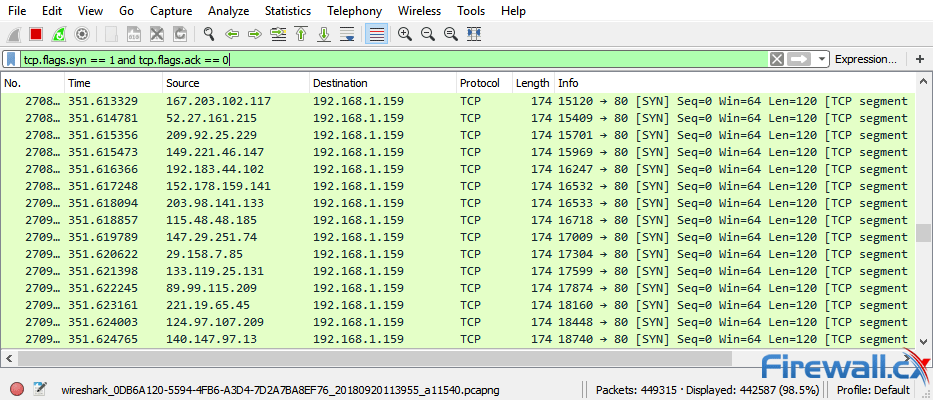
On Investigating the Effectiveness of Biometric Readers in Thwarting Network Attacks: A Secure Architecture Design Proposal