ILP security optimization method for embedded systems with timing constraints | Proceedings of the Seventh Annual Workshop on Cyber Security and Information Intelligence Research

Inductive Logic Programming: 26th International Conference, ILP 2016, London, UK, September 4-6, 2016, Revised Selected Papers by James Cussens
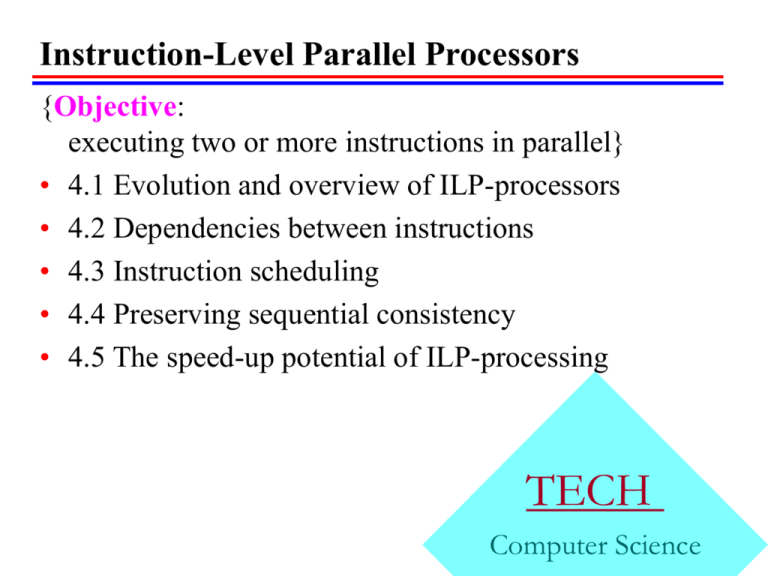
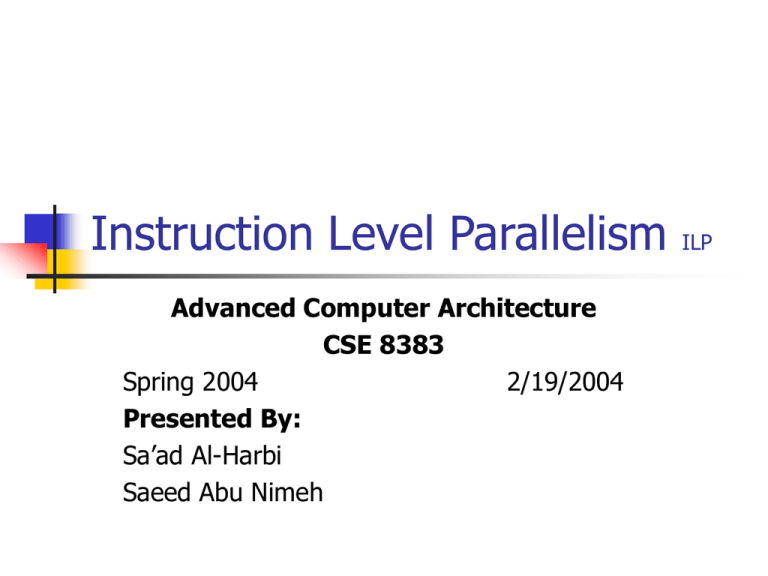
Cleveland State University Department of Electrical Engineering and Computer Science EEC 581 Computer Architecture, Fall